20
Jan 2011
The Dark Side of the Internet – What to Do If Your Site is Attacked!
By Bob Speyer – Web Success Team
Imagine one morning you log on to your website only to find it has been suspended by Google. Without warning, your informative home page has been replaced by a Google Alert page that reads:
“This Connection is Untrusted”
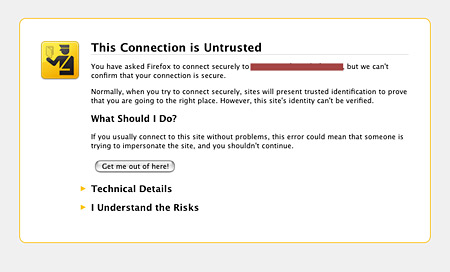
“You have asked Firefox to connect securely to www.xxxxxx.com, but we can’t confirm that your connection is secure. Normally, when you try to connect securely, sites will present trusted identification to prove that you are going to the right place. However, this site’s identity can’t be verified.
What Should I Do?
If you usually connect to this site without problems, this error could mean that someone is trying to impersonate the site, and you shouldn’t continue.”
This article is not intended to scare you, but rather to show you that the Internet can be a very nasty environment and that this could happen to your website at any time.
Internet Wars: May the Google Force Be With You
Generally, malware is installed onto a website because someone hacked into the FTP server or got the login information from the owner’s email. More often than not, a website is hacked through your own email account. Therefore, it is extremely important to remove any sensitive information from your email.
Unfortunately, one of our client websites, not hosted by us, was attacked and suspended two months after launch when it was previously Google compliant and functioning perfectly. The site was compromised by a hacker who placed a malicious script or virus (malware) into the coding which could then cause users’ computers to be infected. Google then informed us that the solution would be to remove the offending (and usually hidden) content from the web pages, and identify the problem and correct the vulnerability.
Once the site has been fixed and secured, you can request that the warning be removed by visiting My Site’s Been Hacked and then asking for a review. If the site is no longer harmful to users, Google will remove the warning and the site will be reinstated.
The Solution to Stopping Malware!
When our client brought the Red Alert to our attention, we thoroughly reviewed the site. We found no obvious Malware scripting, but something external triggered the alert. Since we always keep a clean back-up copy of clients’ websites, we decided to upload the original files to their ftp site and replace the entire web contents – in essence, performing a clean install. Then we resubmitted it to Google and their partner, Stop Malware for a new review and approval. Even before Google’s approval, the site was live at once and functioning properly as soon as we replaced the corrupted files. The offending Alert page was gone (hopefully forever).
The Best Place to Find Help
In order to help prevent future attacks, we attached Google Webmaster Tools to monitor the site and its activity. We submitted the site to Malware Busters and informed the client to change his password on their FTP site as a further precaution.
Please understand that Malware (aka spyware, malware, adware) can also come in the form of malicious user-contributed content or content from an ad network that has an offending advertiser. If you have unwittingly downloaded malware and your computer is compromised, please visit the Stop Malware site for information on how to remove the offending content. The site is also excellent for tips on cleaning and securing your site and, as in the case of our client, how to submit your site for review and re-approval by Google.
Prevention Tips
There are a few things you can do to prevent malware
- Use Mozilla Firefox instead of Internet Explorer, which is more susceptible.
- Keep your anti-virus software up-to-date
- Put a firewall on your computer
- Use physical firewalls by not connecting directly to public IPs
Many hosting providers typically do not find out about malware users until the site is already infected. This is because their security systems are not actively monitoring the system’s activity. For trusted hosting providers, we recommend for Apache environment: Web Hosting Logic and Twintel Solutions.
Knowing that attacks could happen to any site at anytime is a bit disconcerting. It would be great if Google would identify the offending content, or give us 24 hours to correct the problem instead of just a surprise suspension and red alert notice. Never-the-less, being aware of what to do and to act quickly will save you time, worry and money.












July 20th, 2011 16:34 /
Monitoring a website for hacks is free and easy using Google. I created this nice video to show how easy it is using Google Alerts:
https://www.youtube.com/watch?v=kGpCE_eiLNg
Enjoy!